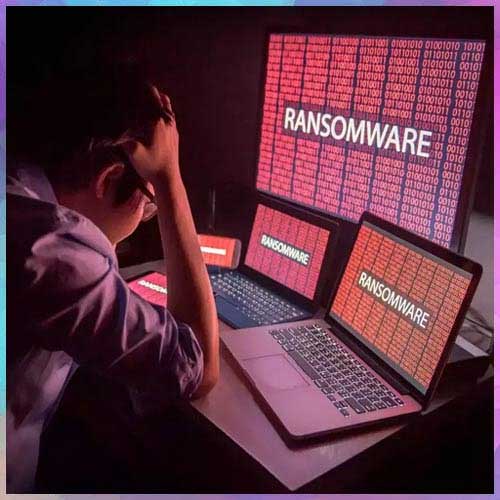
Subex has been closely working with technology and telecom companies to help deploy integrated security solutions to improve the holistic approach towards malwares. Subex’s unique honeypot network has been implemented to better detect threats and anomalies and to counteract ransomware and malware attacks. Kiran Zachariah, VP- IoT Business Solutions, Subex discusses with VARINDIA of how Subex’s honeypot network works, and its offerings in the IoT space -
What is a honeypot network and how does it work?
A honeypot network is a series of physical or virtual devices that are exposed with minimal or no security to the internet with the objective of attracting attacks from hackers and malware. The set-up mimics a likely target of a cyberattack and helps cybersecurity teams gather gain information on the modus operandi of cybercriminals and also aids in studying the ways in which various malware operate so that they can easily be detected and flagged in systems and networks in the future in case of a cyberattack.
Given the recent spate of cyber-attacks and threats that have surfaced of late, how can creating a honeypot network be a solution to it?
Honeypots can be used to gather threat intelligence and they can also serve as decoys to prevent criminals from attacking a legitimate target. Without honeypots, our ability to gather real-time intelligence on the threat environment surrounding the internet will be seriously impaired.
How is a honeypot network different from other fraud detection technologies and solutions?
Depends on what we are comparing a honeypot with. At the highest level, honeypot is also a tool to protect systems and data from cyberattacks. Specifically, a honeypot as the name suggests, serves to attract attacks and more the number of attacks, better is the honeypot and better will be the threat intelligence.
Security of IoT applications is a subject of major concern. What offerings does Subex have in the IoT security space and how it is different from other players?
We offer Subex Secure a hardened IoT security solution along with IoT security consulting, vulnerability assessment and penetration testing, IoT labs and services around IoT security. We are a IoT focused vendor and today, we run one of the largest honeypot networks in the world which elevates our threat intelligence gathering ability. Today, Subex is uncovering some of the latest threats surrounding IoT deployments. Our threat research capabilities are unmatched as are the diversity of the work we do in the IoT space.
What trends do you foresee in the IoT security area in coming times and how does Subex propose to address it?
Targeted attacks, crypto mining and risky insider activity are all emerging threats. Our solution, advisory services and services portfolio are geared to address such threats. Other than this, we do advise businesses, government, educational institutions and other stakeholders to maintain a high level of vigilance on their networks and systems. Honeypots are also a way to deflect attacks. Finally, high levels of security sensitivity across all levels and a willingness to admit that we are on the radar of hackers at all times also helps. A single breach is enough to set the clock back for businesses by years. Loss of IP, customer data, capital and credibility can lead to losses that can harm not just businesses but also nations. Action on cybersecurity driven by caution and diligence is what we need.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.