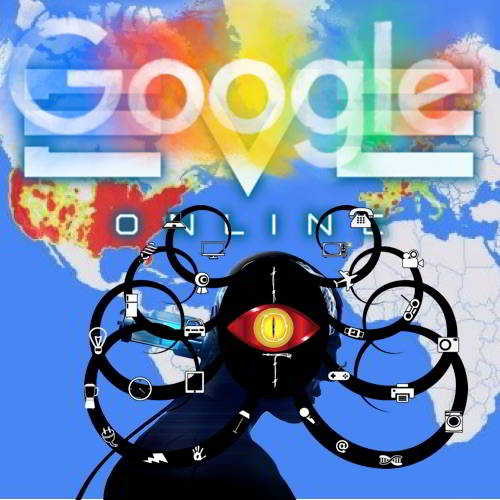
An enormous ad fraud botnet 3ve (Pronounced as Eve) the fake clicks were used to trick online advertisers for years and make tens of millions of dollars as a result,was active since 2014 but could have been around for longer and forced to shut down after 1.7 million PCs were infected to falsify 12 billion ads per day. Plus, Microsoft warns of ‘inadvertently disclosed digital certificates’ that could allow man-in-the-middle attacks.Activity from the group increased in 2017, becoming a huge business with greater than $30 million in profit last year.
According to Google and multiple cybersecurity firms, the ad-fraud scheme has been named 3ve because it relies on a set of three distinct sub-operations, “Each taking unique measures to avoid detection, and each built around different architectures using different components. Its operators constantly adopted new ways to disguise 3ve’s bots, allowing the operation to continue growing even after their traffic was blacklisted. Whenever they were blocked off in one place, they’d reappear somewhere else,” Google said.
A massive team of security companies and federal agencies worked together to shut down an enormous click fraud operation. Although 3ve, started as a small botnet, by the time it was sink holed, it was using 1.7 million infected computers to falsify billions of ad views, which resulted in businesses paying over $29 million for ads that no real human internet users ever saw.
A Google-released whitepaper (pdf) revealed that “3ve generated between 3 billion and 12 billion or more daily ad bid requests at its peak.” When announcing the unsealing of a 13-count indictment against eight defendants, the Department of Justice said the FBI took control of 31 domains and took information from 89 servers that were part of the botnet infrastructure engaged in digital advertising fraud activity.
Google, the FBI, ad-fraud fighting company WhiteOps and a collection of cyber security companies worked together to shut down 3ve. Meanwhile, the United States Department of Justice (DoJ) also unsealed Tuesday a 13-count indictment against 8 people from Russia, Kazakhstan, and Ukraine who allegedly ran this massive online advertising scheme.
The 3ve botnet scheme deployed different tactics, such as creating their own botnets, creating fake versions of both websites and visitors, selling fraudulent ad inventory to advertisers, hijacking Border Gateway Protocol (BGP) IP addresses, using proxies to hide real IP addresses, and infecting users PCs with malware-all to create or generate fake clicks over online ads and get paid. “Tech-savvy fraudsters try to produce fake traffic and fraudulent ad inventory to trick advertisers into believing that their ads are being seen by actual, interested users,” WhiteOps researchers said. 3ve involved 1.7 million computers infected with malware, over 80 servers in generating fake internet traffic, more than 10,000 counterfeit websites to impersonate legitimate web publishers, and over 60,000 accounts selling ad inventory via more than one million compromised IP addresses to generate 3 to 12 billion of daily ad bid requests at its peak.
Google uncovered the 3ve operations last year while its companies were assessing the impact of the Methbot operation, an underground ad fraud enterprise that White Ops revealed in 2016, which ESET named as the Boaxxe botnet.
However, after 3ve’s activity grew in 2017, generating billions of daily ad bid requests, Google collaborated with other security companies who were independently investigating this prominent ad-fraud operation to take down the entire 3ve network.
Google and other security firms worked with the FBI to shut down the massive ad-fraud operation. After obtaining warrants last month, the FBI seized 31 internet domains and 89 servers that were all part of the 3ve infrastructure.
With Ref: Google white paper
Types of three 3ve Operation :
I. 3VE.1-The BOAXXE Malware Scheme
The first 3ve’s three ad fraud sub-operations, called 3ve.1 for the sake of clarity, was powered by a network of bots operating in data centers across the US and Europe.
This operation used the Boaxxe botnet, also known as Miuref and Methbot, and BGP hijacking to obtain IP addresses used for proxying the traffic from the infected devices in the data centers and visit fake and real web pages.
Initially, all the fake ad requests originated from desktop browsers, but over time, this operation increasingly started relying on spoofed mobile traffic from Android devices-ad-requests spoofed to look like they came either from mobile apps or from mobile browsers.
Between September 2014 and December 2016, this scheme used 1,900 computer servers hosted in commercial data centers to load ads from advertisers on over 5,000 counterfeit websites, generating millions of dollars in profit for its operators.
II. 3VE.2-The KOVTER Malware Scheme
This approach used counterfeit domains to sell fake ad inventory to advertisers. However, instead of relying on proxies to hide its activities, this approach deployed a hidden, custom browsing agent (Chromium Embedded Framework) on more than 700,000 computers infected with the Kovter malware.
This scheme made use of redirection servers that instructed the infected computers to visit specific fake web pages.
Detected by ESET in 2014, Kovter was initially a piece of ransomware, but the family has evolved since then to become ad fraud malware with its ability to send fake traffic if it detects a network monitor, terminate its own spawned process if Windows Task Manager is started, use so-called “fileless” persistence by storing its malicious payload encrypted in the Windows registry, and more.
III. 3VE.3-Data Centers IPs as Proxies
The third 3ve-associated sub-operation was similar to 3ve.1. Its bots were based in a few data centers, but in order to cover its tracks, it used the IP addresses of other data centers as proxies (exit node layer) instead of residential computers.
Although data centers are far more suspicious to advertisers who are worried about bot traffic, 3ve.3 strategy still allowed a reasonable degree of agility by helping its operators find new data centers as soon as old data centers were blocked.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.