India has been one of the largest mobile market in the world with a huge potential. It is estimated that more than a billion smartphones will be sold in next five years, taking the number of users to surpass 700 million by 2022. It is a device that has completely changed the way people used to access information and services. It has become the primary device which contains an individual’s necessary information which can be exploited by the cyber criminals for their benefits.
“India has seen an incredible growth of mobile usage, it is estimated that more than a billion smartphones will be sold in India over the next five years, taking the number of users to surpass 700 million by 2022. Mobile phones have democratized how people access information and services. More and more people are using various applications on mobiles to access services, social media, and ecommerce sites, we see a rising trend in app-centricity. There are multiple apps being used by a single individual.
It is said that a single person uses at least 40 applications a month. Most often to have a fuss-free experience while using an app, people often store their card details or use their existing accounts to log in. These come at a price – in terms of privacy and application security. According to F5 Network’s 2018 Protecting Applications Report India is seen as the country least mindful about security when it comes to app usage, with only 49 percent prioritizing security over convenience.
 This lack of caution provides attackers with a larger surface area to strike and this is further aggravated by the fact that multiple devices are interconnected and have confidential information saved. In fact, just last year, some 3.3 million malicious apps were detected in Asia Pacific the highest number globally. To reinforce this point, research from a threat intelligence lab revealed that in 86 percent of the 443 breaches detected over the last decade, attackers had targeted apps and/or used stolen credentials. Similarly, applications were also the initial targets of 53 percent of breaches,” upholds Mohan Veloo, CTO, F5 Networks.
This lack of caution provides attackers with a larger surface area to strike and this is further aggravated by the fact that multiple devices are interconnected and have confidential information saved. In fact, just last year, some 3.3 million malicious apps were detected in Asia Pacific the highest number globally. To reinforce this point, research from a threat intelligence lab revealed that in 86 percent of the 443 breaches detected over the last decade, attackers had targeted apps and/or used stolen credentials. Similarly, applications were also the initial targets of 53 percent of breaches,” upholds Mohan Veloo, CTO, F5 Networks.
Mobile Security landscape
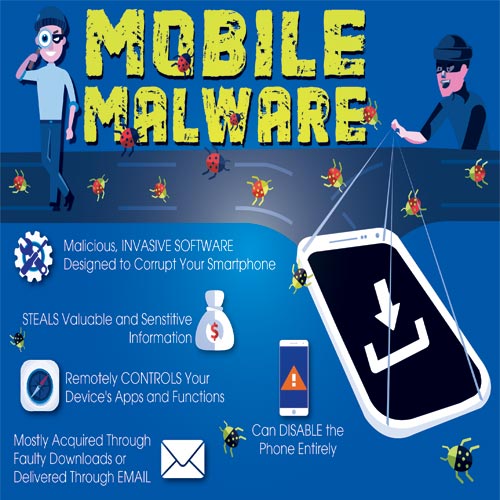
We are currently living in a Digital era where mobility and IoT impacted the world in a big way. Both the technologies are making people’s life easy by encouraging innovation and driving productivity. By virtue of these technologies users can access corporate network and resources anytime and anywhere. But mobility also poses serious challenges for organizations by eradicating traditional security architectures and protective mechanism.
 “In today’s mobile and IoT era, as mobility drives innovation and productivity, it also creates serious challenges by breaking traditional security architectures and protective mechanisms. This growing influx of mobile and IoT devices coupled with greater reliance on cloud-based applications has a profound impact on the IT security of organizations specially in the form of surreptitious Malwares,” says Santanu Ghose, Director – India, Aruba, a Hewlett Packard Enterprise company.
“In today’s mobile and IoT era, as mobility drives innovation and productivity, it also creates serious challenges by breaking traditional security architectures and protective mechanisms. This growing influx of mobile and IoT devices coupled with greater reliance on cloud-based applications has a profound impact on the IT security of organizations specially in the form of surreptitious Malwares,” says Santanu Ghose, Director – India, Aruba, a Hewlett Packard Enterprise company.
Indian is one of the largest app markets in terms of downloading. The app makers are gradually making the apps according to Indian consumer’s needs with local customizations and features. The F5 Network study also brings forth that 72% of Indians favour mobile over desktop. This also increases security concerns.
Elaborating on the same, Mohan Veloo of F5 Networks says, “India’s mobile app market is the second-largest by downloads in the world. App makers across the globe are vying to make their apps more Indian consumer friendly by adding more local customizations and features unique to the Indian consumer base. Security concerns rise with the upsurge of automation and digitization. Lack of proper password management and digital hygiene compound security issues for personally held devices such as mobiles that are connected to various interfaces and can call upon other apps to push, pull or process data.”
The device becomes a rich computing environment that includes potentially everything such as - our digital persona, our passwords, the keys to our home or rather, access to our entire digital life including all the connected things in our home. Because of this, our mobile phones have become a very lucrative platform for cyber threats, providing hackers, a direct route into the users’ lives.
 Venkat Krishnapur, Vice-President of Engineering and Managing Director, McAfee India highlights, “Findings from the ‘McAfee Mobile Threat Report’, state that today, there are more than 4,000 mobile threat families and variants in the McAfee sample database. These sheer numbers tell us how the threat landscape is ever evolving and that, our mobile phones are becoming one of the foremost targets for cybercrimes.
Venkat Krishnapur, Vice-President of Engineering and Managing Director, McAfee India highlights, “Findings from the ‘McAfee Mobile Threat Report’, state that today, there are more than 4,000 mobile threat families and variants in the McAfee sample database. These sheer numbers tell us how the threat landscape is ever evolving and that, our mobile phones are becoming one of the foremost targets for cybercrimes.
Mobile malware authors are increasingly aiming for and generating revenues amounting to millions of dollars with their malicious campaigns. So, the pace at which malware has evolved on mobile devices is alarming."
Most Affected OS
As the use of mobiles is increasing with the passing days it is becoming easy for the cyber criminals to exploit the devices. It has been observed that Android operating system based devices have experienced mobile malware attacks more when compared to Apple iOS.
 Continuing on this Rajesh Maurya, Regional Vice President, India & SAARC, Fortinet says, “According to Fortinet Threat Landscape Report for Q3 2018 over one-quarter of organizations experienced a mobile malware attack, with the majority being on the Android operating system. In fact, of the threats organizations faced from all attack vectors, 14% of total malware alerts were Android related. By comparison, only .000311% of threats were targeted at Apple iOS. Mobile threats are a looming threat that must be addressed, especially as the mobile-shopping and Mobile payments are gaining popularity. These threats can become a gateway for corporate networks to be exploited. Criminals know mobile is an accessible target for infiltrating a network, and they are exploiting it.”
Continuing on this Rajesh Maurya, Regional Vice President, India & SAARC, Fortinet says, “According to Fortinet Threat Landscape Report for Q3 2018 over one-quarter of organizations experienced a mobile malware attack, with the majority being on the Android operating system. In fact, of the threats organizations faced from all attack vectors, 14% of total malware alerts were Android related. By comparison, only .000311% of threats were targeted at Apple iOS. Mobile threats are a looming threat that must be addressed, especially as the mobile-shopping and Mobile payments are gaining popularity. These threats can become a gateway for corporate networks to be exploited. Criminals know mobile is an accessible target for infiltrating a network, and they are exploiting it.”
 On similar lines Debasish Mukherjee, Country Manager India & SAARC, SonicWall puts forward, “We track mobile malware attack attempts on the global SonicWall installed base. So far, in 2018, SonicWall Capture Labs detected over 133 million attack attempts on Android devices, up from a total year count in 2017 of 64m. And, another data point, Android accounted for 21% of the never-before-seen malware detected by SonicWall Capture ATP using Real-Time Deep Memory Inspection in September of this year. So, this is a huge and growing problem.”
On similar lines Debasish Mukherjee, Country Manager India & SAARC, SonicWall puts forward, “We track mobile malware attack attempts on the global SonicWall installed base. So far, in 2018, SonicWall Capture Labs detected over 133 million attack attempts on Android devices, up from a total year count in 2017 of 64m. And, another data point, Android accounted for 21% of the never-before-seen malware detected by SonicWall Capture ATP using Real-Time Deep Memory Inspection in September of this year. So, this is a huge and growing problem.”
 Diving deep into it Sunil Kriplani, Senior Vice President (Global Sales and Marketing), eScan opines, “The penetration of mobile malware is marginally low when compared with the PC based malware. Recently there has been an increase in the take-down of Fake Apps existing on Playstore by Google. Mobile/Android-based malware are existing due to the sheer fact that the policies of Google Playstore aren’t as stringent as those of the Apple Store. Furthermore, side-loading of Android-based apps is relatively very easy when compared with iOS, hence Android-based malware shall thrive and continue to grow for years to come.”
Diving deep into it Sunil Kriplani, Senior Vice President (Global Sales and Marketing), eScan opines, “The penetration of mobile malware is marginally low when compared with the PC based malware. Recently there has been an increase in the take-down of Fake Apps existing on Playstore by Google. Mobile/Android-based malware are existing due to the sheer fact that the policies of Google Playstore aren’t as stringent as those of the Apple Store. Furthermore, side-loading of Android-based apps is relatively very easy when compared with iOS, hence Android-based malware shall thrive and continue to grow for years to come.”
Types of launching a threat
The cyber criminals use various innovative ways to launch a threat on the mobile device. The popular ways are through mobile ads, keylogger, ransomware. Explaining the different types of malwares, Venkat Krishnapur of McAfee India says, “Malware can find its way onto your mobile device through mobile ads that accompany a significant amount of content and cybercriminals have turned their attention toward using them to spread malware to unsuspecting users. These “malvertisements” are often delivered through legitimate ad networks and may not appear outright spammy, but can contain Trojans or lead to malicious websites when clicked on.
A keylogger, or keystroke logger, is a software that tracks the keystrokes performed on a mobile device usually with the intent to steal account information, credit card numbers, and other private data. Security researchers claim that a flaw in the way certain apps run while in the background, can be utilized to monitor what you type onto the touchscreen. Often, these threats are delivered through bad mobile apps, masquerading as something authentic. Most of these treacherous apps can be found on less-than-reputable third-party app stores.
Ransomware is perhaps the most devious mobile malware tactic through which hackers can gain access to photos, videos, and other personal information until the ransom is paid to the hacker. Another harmful form of malware is Trojans. Trojans masquerade as harmless applications, tricking users into downloading and using them. Once successively installed, they then can steal personal data, crash a device, spy on the users’ activities, or even launch a DDoS attack.”
 Sanjit Chatterjee, CEO, REVE Antivirus says, “There are several ways of launching threat in a mobile device starting from Trojan attack, Botnet to Malvertising. Trojans usually pose as legitimate applications, which are downloaded in ignorance. Trojans may be clubbed with a free software and gets activated when the program is installed. Apart from Trojans, we have analysed that infections through Botnets have also increased.”
Sanjit Chatterjee, CEO, REVE Antivirus says, “There are several ways of launching threat in a mobile device starting from Trojan attack, Botnet to Malvertising. Trojans usually pose as legitimate applications, which are downloaded in ignorance. Trojans may be clubbed with a free software and gets activated when the program is installed. Apart from Trojans, we have analysed that infections through Botnets have also increased.”
With the growing penetration of mobiles in the country, the mobile security landscape is becoming quite distressing as low awareness on mobile security is increasing the number of threats. People are falling easy prey to cyber criminals. Mobile based threats includes Banking Trojans, cryptomining etc. Cyber criminals are also using instant messaging apps, social engineering and adware are few popular ways of launching a threat.
“The situation is quite alarming, mostly due to the low awareness about the need for adequate security amongst mobile users. The increase in the number of mobile-based threats such as Banking Trojans and cryptomining attacks is indicative of a growing shift towards exploiting vulnerable mobile devices to compromise sensitive personal information.
Instant messaging apps are also fast becoming a conduit for spam messages and fake offers, which are basically phishing attacks which lure users into clicking on malicious links with the intent of stealing sensitive data and gaining control over their devices. This is in addition to the phishing emails and SMS used by hackers to trick users into clicking on a malicious link. Another major method employed to compromise a mobile phone is social engineering.
 Adware have also become a prominent threat, with cybercriminals leveraging them aggressively to display ads to users and generate more revenue. What’s particularly alarming about adware, despite being seemingly harmless, is that they have the capability to collect device info like IMEI, phone number, bookmarks etc. This information can then be leveraged to launch highly-targeted spear phishing and social engineering attacks,” explains Sanjay Katkar, Joint Managing Director and Chief Technology Officer, Quick Heal Technologies.
Adware have also become a prominent threat, with cybercriminals leveraging them aggressively to display ads to users and generate more revenue. What’s particularly alarming about adware, despite being seemingly harmless, is that they have the capability to collect device info like IMEI, phone number, bookmarks etc. This information can then be leveraged to launch highly-targeted spear phishing and social engineering attacks,” explains Sanjay Katkar, Joint Managing Director and Chief Technology Officer, Quick Heal Technologies.
Financial Services Industry on the radar
It's no secret that the financial services industry is a top target for cybercriminals looking to steal valuable data. This growing risk comes at a time when financial services firms are turning their focus to innovating new technologies and features to meet evolving consumer demands.
To offer better services to its customers, banks have come up with Mobile banking apps which gave respite to customers from going to bank for any kind of transaction. However, with India becoming a digital economy, every sector, including banking has witnessed malware attacks.
“Banking malware codes are specifically designed to steal financial information and transfer funds to their bank accounts. In infected devices banking malwares first search for banking or payment apps and then create a fake pop-up overlay page. Once users open them to enter their credentials the information is sent directly to the attacker's servers. For example, the Marcher banking malware discovered by Check Point superimposed a fake credit card payment page over the original one to steal credit card information and bank credentials that it relayed to an external server.
 Another source of banking malware is through the device’s app store itself where fake apps of many payment and banking vendors exist and show up for downloading. A prime example is the BankBot Trojan that was first detected by Check Point. The Trojan was programmed to embed itself in the codes of various apps on the Google Play Store. Once it was downloaded by the unsuspecting user, the hidden banking malware asked for accessibility permissions that granted it almost complete control over the device,” defines Venugopal N, Director-Security Engineering, Check Point Software Technologies, India & SAARC.
Another source of banking malware is through the device’s app store itself where fake apps of many payment and banking vendors exist and show up for downloading. A prime example is the BankBot Trojan that was first detected by Check Point. The Trojan was programmed to embed itself in the codes of various apps on the Google Play Store. Once it was downloaded by the unsuspecting user, the hidden banking malware asked for accessibility permissions that granted it almost complete control over the device,” defines Venugopal N, Director-Security Engineering, Check Point Software Technologies, India & SAARC.
In the banking industry, mobile banking Trojans falls under the well-known malwares. These kind of malwares are designed to loot money directly from mobile user’s bank accounts and the cyber criminals prefer these kind of attacks as it is an easy profit for them. Further explaining Shrenik Bhayani, General Manager, Kaspersky Lab (South Asia) says, “Mobile banking Trojans are one of the most infamous type of malware, as they are designed to steal money directly from mobile users’ bank accounts. This type of attack is attractive to cybercriminals from all over the world, looking for an easy profit. The malware is typically disguised as a legitimate app, to lure people into installing it. Once the banking app is launched, the Trojan displays its own interface overlaying the banking app’s interface. When the user inputs credentials, the malware steals the information.

The second quarter of 2018 experienced a massive influx of these types of Trojan at 61,045, which is a historic high in all the time that Kaspersky Lab has been observing such threats. The greatest contribution to the number was made by the creators of Trojan Hqwar, with about half of the new modifications discovered relating to this malware. Trojan Agent took second place with around 5,000 packages.”
To sum up
Hackers will continue to scale up their ways of launching attacks. With time, they will come up with different sophisticated threats which will be more infamous and damaging. Though banks are taking required steps to fortify its security ecosystem hackers are also upping their game with innovative ways of attacks. Lack of awareness among the mobile users is the prime reason behind the increased rate of cyber attack. It is our responsibility to use mobile devices wisely so that we do not become an easy victim.
It is therefore important that customers observe necessary security safeguards using their smartphones such as: strong passwords, staying alert when an app asks for permission to gain access to your mobile device, ensuring that you are using your bank’s official app and not falling prey to a fake one and by never clicking on a link sent to you by the name of ‘Your Bank’, to name a few.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.