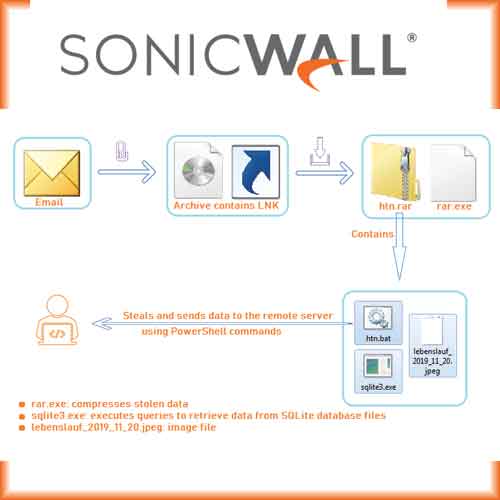
SonicWall RTDMI engine has recently detected a Windows shortcut file capable of downloads and executing LALALA infostealer to the user’s device.
LALALA info stealer is a batch script, which takes the help of PowerShell to steal and send the victim's data to the server. The irony however is that, this sort of an attack is detected by only a few security vendors on popular threat intelligence sharing portal. This is yet another classic instance of Malware authors’ using simple but very effective approaches to stay low and steal user’s data.
The malware usually processes the data on the victim's machine to extract very precise information which is sent to the malware server. But LALALA sends good amount of data to the server which needs further processing at the server's end to extract the operative data. The malware decrypts some application’s data (eg. Google Chrome and Microsoft Edge) on user’s device which uses Windows logon based encryption because that data cannot be decrypted on the other machine.
“As the new age mantra stresses that Data is the new oil is encouraging cyber-attackers get innovative in their approach to steal data. They are going beyond regular methods and using unsuspecting yet popular platforms such as Google Chrome and Microsoft Outlook as the launch-pad to prowl on unsuspecting users. This situation calls for effective cyber-security mechanisms to be activated. It becomes imperative, for cyber security solution providers to innovate and create a response mechanism at a rapid pace,” says Debasish Mukerjee as VP, Regional Sales -APAC at SonicWall.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.