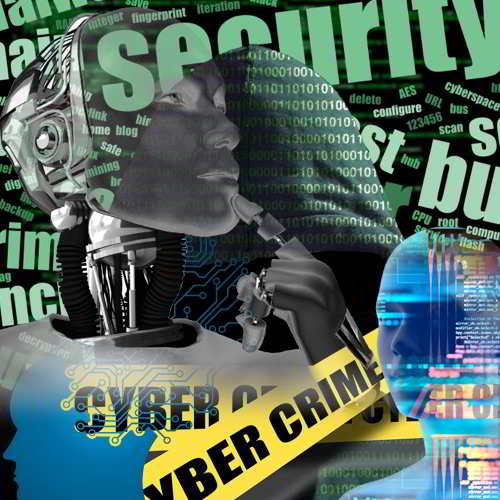
Data protection attempts are becoming more and more challenging, as the attackers get equipped with sophisticated hacking attempts powered by Artificial Intelligence (AI) and machine learning (ML). These advanced technologies are computer algorithms, based on an analytical model designed to collect data and adapt its processes and activities according to use and experience, getting more smarter over time.
These hacking algoritms also automate the time-consuming cyberattacks with hackboats, and include social media pishing and email pishing etc. The U.S. intelligence community reports that cybercriminals are even using stolen computing resources to eliminate the main costs of ML - central processing unit (CPU) time, graphics processing unit (GPU) time, data transfer and the electricity they all consume.
As per a predictions report for 2019 revealed by Tend Micro - 'Mapping the Future - Make the users' aware that attackers will increase the effectiveness of proven attack methods by adding more sophisticated elements to take advantage of the changing technology landscape. “As we head into 2019, organizations must understand the security implications of greater cloud adoption, converging IT and OT, and increasing remote working,” said Greg Young, vice president of cybersecurity for Trend Micro. “Cybercriminals will continue to follow a winning formula – exploiting existing flaws, social engineering and stolen credentials – to drive profits. As both the corporate attack surface and unknown cyber threats increase, it’s more important than ever for organizations to put more resources behind employee education to help protect against these growing attacks.”
The role of social engineering in successful attacks against businesses and individuals will continue to increase throughout the year. Since 2015, the number of phishing URLs blocked by Trend Micro has increased by nearly 3,800 percent. This offsets the lessening reliance on exploit kits, which has decreased by 98 percent in the same time. Additionally, attackers will continue to rely on known vulnerabilities that remain un-patched in corporate networks for 99.99 percent of exploits, as this remains a successful tactic.
“The full range of known and unknown threats can never be addressed by one single technology. In 2019, enterprises should not look for a silver bullet, but a mix of threat defense techniques that complement each other and work together,” said Nilesh Jain, Vice President, India and Southeast Asia, Trend Micro.
Trend Micro also predicts that attackers will leverage these proven methods against growing cloud adoption. More vulnerabilities will be found in cloud infrastructure, such as containers, and weak cloud security measures will allow greater exploitation of accounts for cryptocurrency mining. This will lead to more damaging breaches due to misconfigured systems.
Attackers will also implement emerging technologies like AI to better anticipate the movements of administration. This will lead to more convincing targeted phishing messages, which can be critical to BEC attacks. Additionally, it is likely that BEC attacks will target more employees who report to C-level executives, resulting in continued global losses.
SIM swapping and SIM-jacking will be a growing threat to take advantage of remote employees and everyday users. This attack method allows criminals to hijack a cell phone without the user’s knowledge, making it difficult for consumers to regain control of their devices. Additionally, the smart home will be an increasingly attractive target for attacks that leverage home routers and connected devices.
Leading businesses already leverage AI and ML algorithms to automate malware scanning and improve their cyber defenses. Many information technology (IT) professionals are experimenting with AI and ML to see how it can improve business processes and increase productivity. What businesses must realize is that cybercriminals are taking the same approach to innovate their methods of attack.
Both cyberattackers and defenders are looking to use artificial intelligence (AI) and ML to gain an advantage.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.