The hackers use a group of four command know as "dictionary attacks." and control servers to send requests to over 14,000 proxy servers provided by a Russian proxy provider called best-proxies[.]ru. controlling a network of over 20,000 already-infected WordPress installations are using these sites to launch attacks on other WordPress sites.They use these proxies to anonymize the control servers traffic. The requests pass through the proxy servers. Those sites are running an attack script which attacks targeted WordPress sites.
The company, which manages and publishes the Wordfence plugin, a firewall system for WordPress sites, says it detected over five million login attempts in the last month from already-infected sites against other, clean WordPress portals.
Between Wordfence’s brute force protection and the premium real-time IP blacklist, we have blocked more than five million malicious authentication attempts associated with this attack campaign in the last thirty days alone.
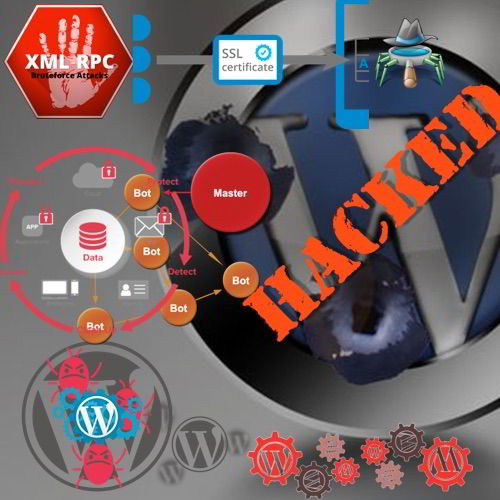
The Defiant Threat Intelligence team recently began tracking the behavior of an organized brute force attack campaign against WordPress sites. This campaign has created a botnet of infected WordPress websites to perform its attacks, which attempt XML-RPC authentication to other WordPress sites in order to access privileged accounts. The attacks are what security experts call "dictionary attacks." These are repeated login attempts during which hackers test a series of username and password combinations, hoping to score a hit and gain access to an account. They discovered that at the top of this botnet stands hydra-like head of four command and control servers that instruct already-infected sites on which other sites to attack.
Defiant security researcher Mikey Veenstra says the company has managed to gain an insight into how this botnet operates.
These scripts read a list of targets they receive from the command and control server, assemble a list of passwords based on a predefined list of password patterns and then try to use the newly generated password to log into another site's admin account.
"If the brute force script was attempting to log on to example.com as the user alice, it will generate passwords like example, alice1, alice2018, and so on," Veenstra explained the attack mechanism in his report. "While this tactic is unlikely to succeed on any one given site, it can be very effective when used at scale across a large number of targets.” Under normal circumstances, because the attackers used a network of proxies to hide the location of their command and control servers, researchers wouldn't be able to track this entire botnet's activity.
Fortunately, Defiant says that the people behind this botnet made "some mistakes in their implementation of the brute force scripts" that allowed researchers to expose the botnet's entire backend infrastructure. Furthermore, the mistakes didn't stop at the brute force scripts. Defiant researchers say they were able to bypass the botnet control panel login system and take a peek inside the crooks' operation.
The IPs performing the brute force attacks were nearly all associated with popular web hosting providers, and that the attacks were all targeting WordPress’s XML-RPC interface at /xmlrpc.php. The User-Agent strings associated with these requests matched those used by applications commonly seen interacting with the XML-RPC interface, like wp-iphone and wp-android. Since these applications typically store credentials locally, it was unusual to see a significant amount of failed logins from them.
The company says it already shared the information it gathered from the botnet with law enforcement. Sadly, the botnet's four command-and-control servers couldn't be taken down, as they are hosted on the infrastructure of HostSailor, a company characterized a while back as a bulletproof hosting provider that doesn't honor takedown requests. This means the botnet is still alive and kicking, continuing to attack more WordPress sites.
The threat actors (hackers) use a group of four command and control (C2) servers to send requests to over 14,000 proxy servers provided by a Russian proxy provider called best-proxies[.]ru. They use these proxies to anonymize the C2 traffic. The requests pass through the proxy servers and are sent to over 20,000 infected WordPress sites. Those sites are running an attack script which attacks targeted WordPress sites.
The diagram below illustrates the attack chain.

How Wordpress becoming Slave for Wordpress site ..???
With this data in hand, when identified the brute force attack, the scripts present on infected WordPress sites matching the attacks were tracked. The scripts target the XML-RPC interface of WordPress sites to test username/password pairs, and randomly spoof the User-Agent string of each request:

The brute force script takes command and control (C2) input via POST in order to define some execution settings, such as a JSON array of targeted domains and a local wordlist to be used:

Central C2 Servers Identified
The attack chain in this campaign made use of multiple layers of abstraction between the attacker and target sites. Brute force attacks are executed by a network of infected WordPress sites, which receive instructions via a network of proxy servers, so it would typically be very difficult to track the central C2 servers behind it all. The attacker made some mistakes in their implementation of the brute force scripts.
Since the scripts each make use of wordlists stored on the same infected WordPress site, they include functionality to regenerate these wordlists if necessary:

The checkWordsList() function is passed a $path argument which defines a remote address containing the wordlist to be used. If the local wordlist is missing, the script will download the list from the given address. This path is provided alongside the rest of the POST data sent from the proxy servers to the brute force script. Requests intercepted by source firewall included this path, which contained an IP address.
This IP pointed to a server which contained a login page.
What to do?
Because of the use of multiple layers of abstraction between the attacker and target sites, botnet's automated login attempts aren't directed at the WordPress login panel, but instead at the WordPress XML-RPC authentication mechanism, changing a site's admin panel URL won't help.
Instead, Defiant recommends that WordPress site owners use a WordPress security plugin that can block brute-force or dictionary attacks carried out against the XML-RPC service.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.






























