Security researchers have uncovered a sophisticated cyber espionage campaign known as Silver Dragon that targets government organizations using phishing, server exploitation, and cloud-based malware infrastructure designed for stealthy, long-term intelligence gathering operations.
Cybersecurity researchers at Check Point Software Technologies have identified a sophisticated cyber espionage campaign targeting government institutions across Southeast Asia and parts of Europe. The operation, named Silver Dragon, has reportedly been active since mid-2024 and appears focused on long-term intelligence gathering rather than financial gain.
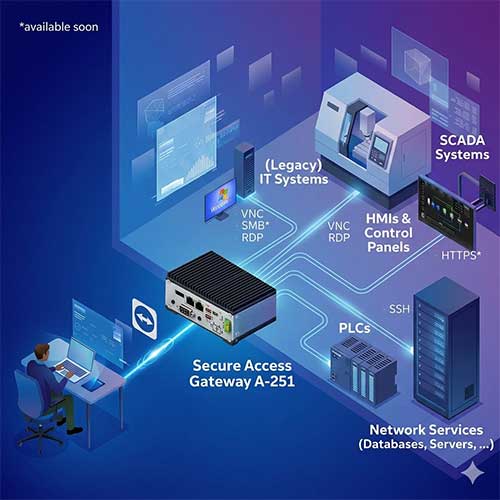
According to the company’s threat intelligence team, the campaign employs a mix of attack methods including phishing emails, exploitation of publicly accessible servers, custom-built malware, and command-and-control infrastructure hosted on trusted cloud platforms.
Researchers believe the activity is likely connected to a Chinese-linked threat group operating within the broader ecosystem of APT41, a well-known advanced persistent threat actor previously associated with cyber espionage operations.
Targeting government networks through multiple entry points
Investigators say most identified victims are government agencies in Southeast Asia, though additional activity has been detected in parts of Europe. The targeting pattern suggests a campaign focused on gathering strategic intelligence rather than causing disruption.
Attackers primarily gain access through two main techniques. The first involves exploiting vulnerabilities in internet-facing servers. Once a server is compromised, attackers can move deeper into internal networks and deploy additional tools to maintain access.
The second method relies on phishing campaigns. In one observed case, attackers sent emails impersonating official communications to government organizations in Uzbekistan. The attachments contained hidden malicious components that executed in the background while displaying harmless documents to victims.
Security analysts note that combining server exploitation with phishing improves the attackers’ chances of infiltrating different types of networks.
Malware uses cloud platforms to avoid detection
One of the most notable elements of the Silver Dragon campaign is its use of a custom backdoor called GearDoor. Instead of connecting to suspicious servers, the malware communicates through files stored on Google Drive.
Each infected device creates a dedicated cloud folder to exchange instructions and upload stolen data. Because traffic to cloud services is typically allowed in corporate environments, the malicious activity can blend with legitimate network traffic.
Researchers also observed additional tools used to collect intelligence, including screenshot capture utilities and remote command execution programs. In several cases, attackers deployed Cobalt Strike, a legitimate penetration testing tool that is frequently abused in cyberattacks.
Security experts warn that the campaign highlights a growing trend in cyber espionage: the use of trusted services and legitimate system processes to remain hidden for extended periods. Organizations, particularly government agencies, are advised to strengthen patch management, monitor system services closely, and improve defenses against phishing attacks.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.